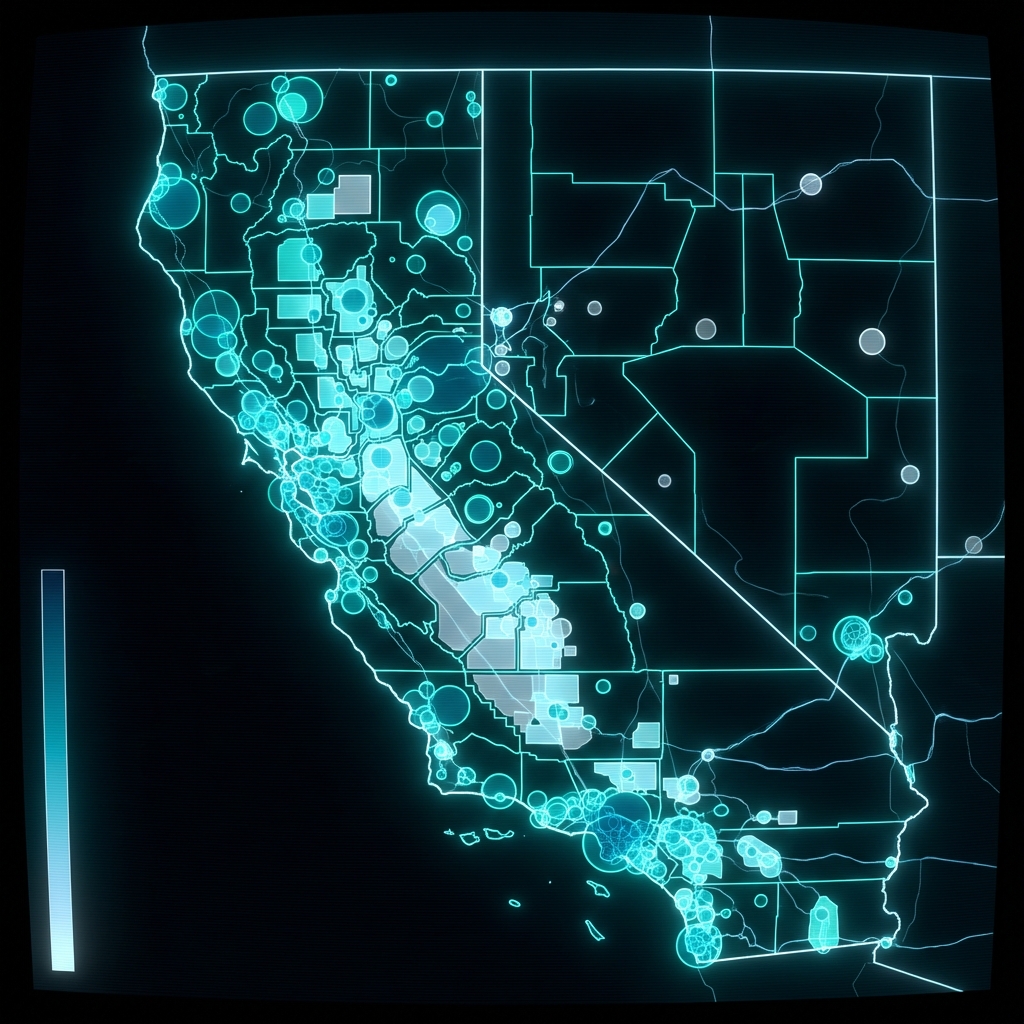
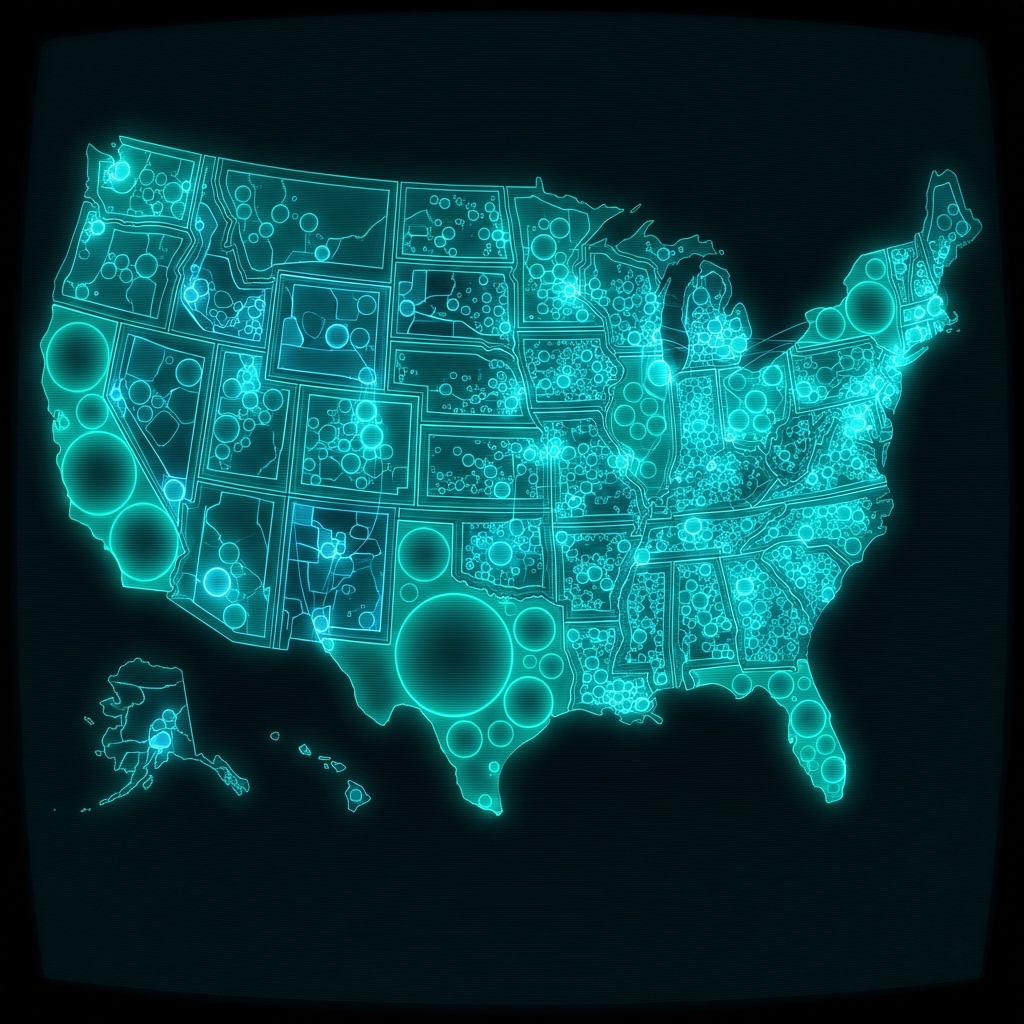
EHR Incentive Program Payments, Hospitals
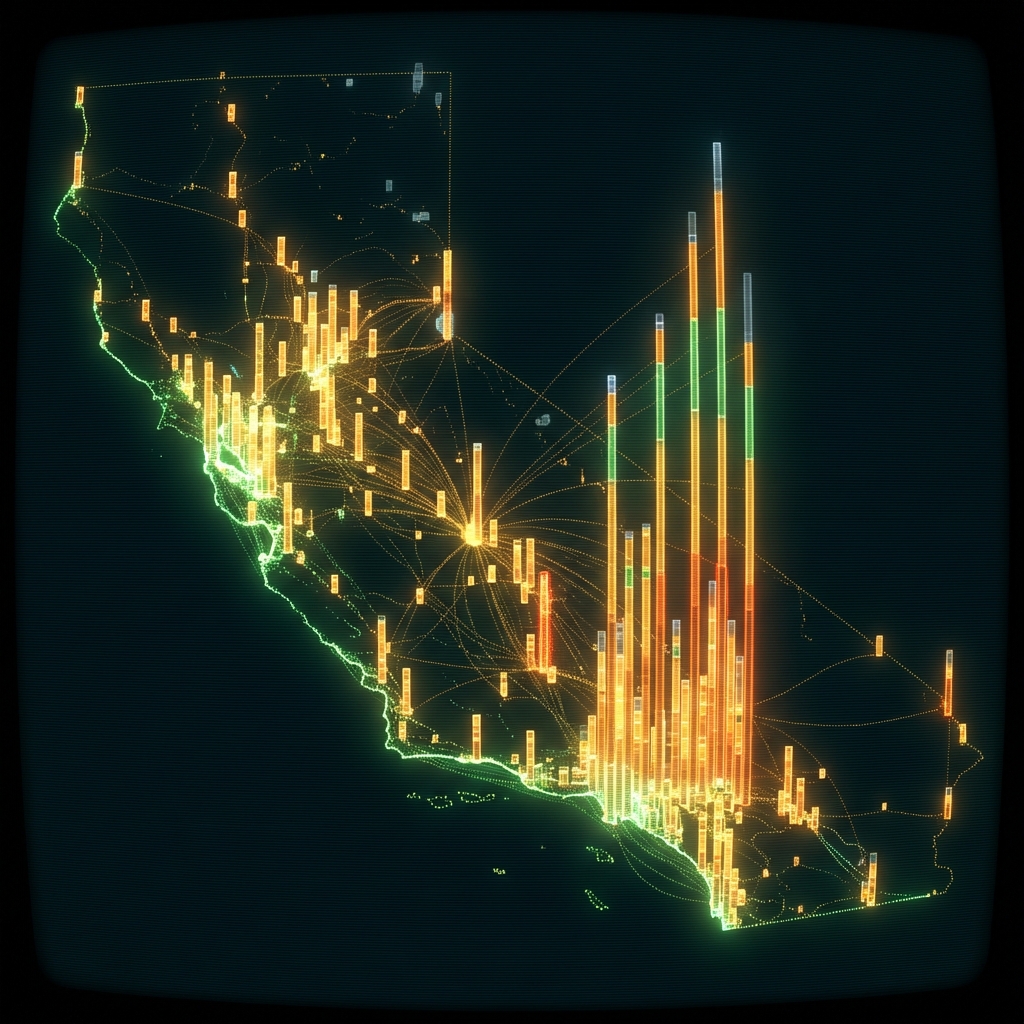
Hospitals that received payments through California's Medi-Cal Electronic Health Record (EHR) Incentive Program for adopting certified EHR systems. Each record includes the hospital's national provider identifier, payment amount, and payment date.
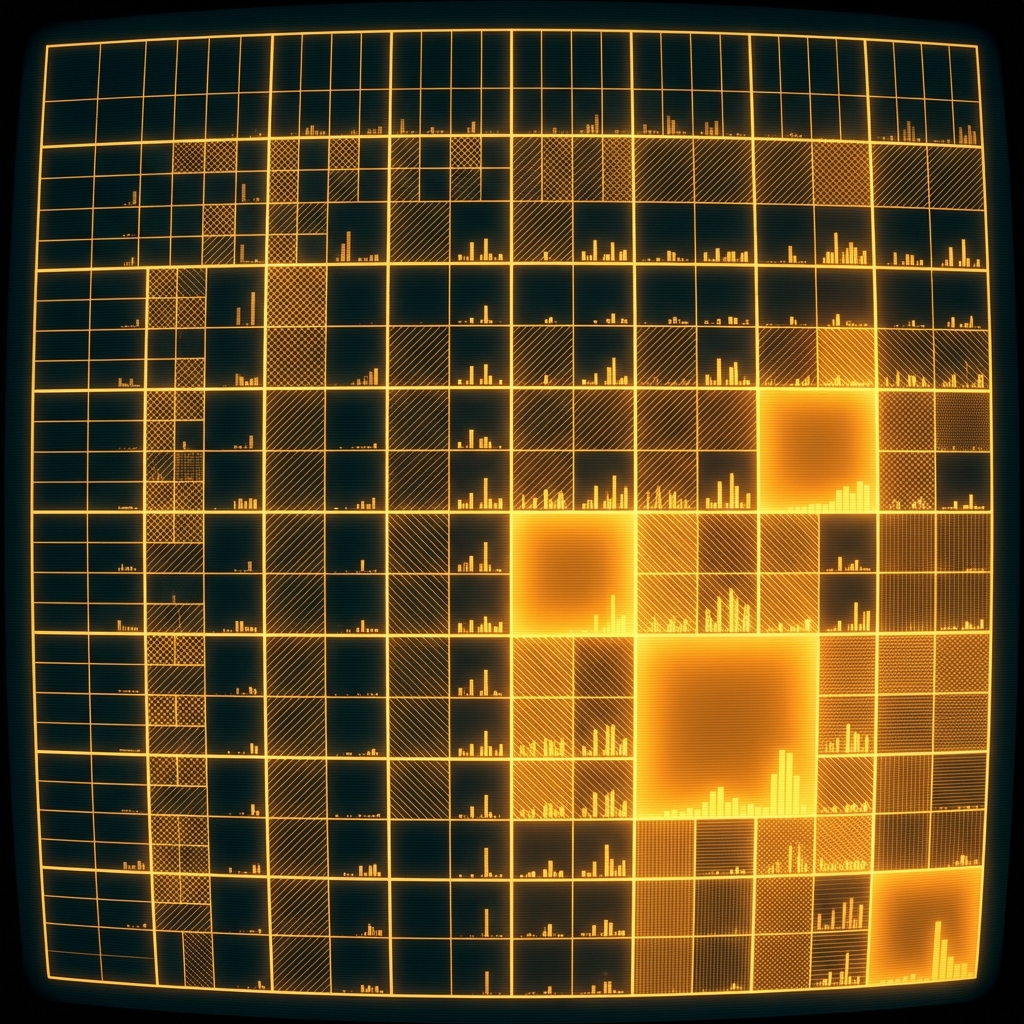
| Namelegal entity | Cityaddress | Stateaddress | ZIP Codeaddress | Street Addressaddress | Xgeospatial | Ygeospatial | Objectididentifier | Npiregistration | Ccnregistration | Business Countyaddress | Payment Year Numberquantity |
|---|---|---|---|---|---|---|---|---|---|---|---|
| Rady Childrens Hospital - San Diego | San Diego | California | 92123 | 3020 Childrens Way, Mail Code 5002 | -117.1520235 | 32.798322 | 323 | 1710065933 | 53303 | San Diego | 4 |
| SHRINERS HOSPITALS FOR CHILDREN | Los Angeles | California | 90020 | 3160 Geneva Street | -118.2864015 | 34.0671780000001 | 322 | 1508908591 | 53310 | Los Angeles | 1 |
| SHRINERS HOSPITALS FOR CHILDREN | Sacramento | California | 95817 | 2425 Stockton Blvd | -121.45545 | 38.5530120000001 | 321 | 1962530451 | 53311 | Sacramento | 4 |
Health IT Vendor Prospecting by EHR Adoption Stage
A sales team at a health IT company selling EHR-adjacent software identifies California hospitals that completed the program under Meaningful Use criteria versus those that only reached the Adopt/Implement/Upgrade stage, prioritizing outreach to the latter as likely candidates for workflow improvement tools.
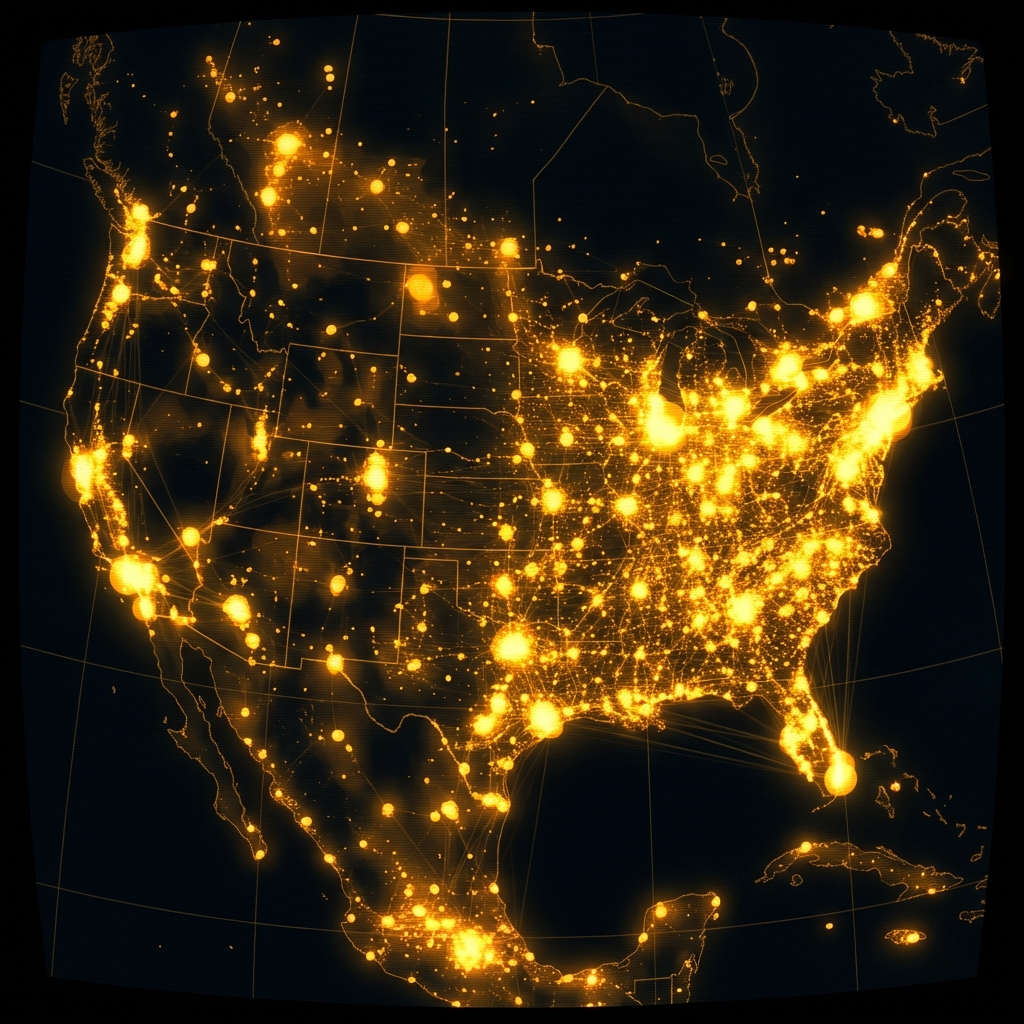
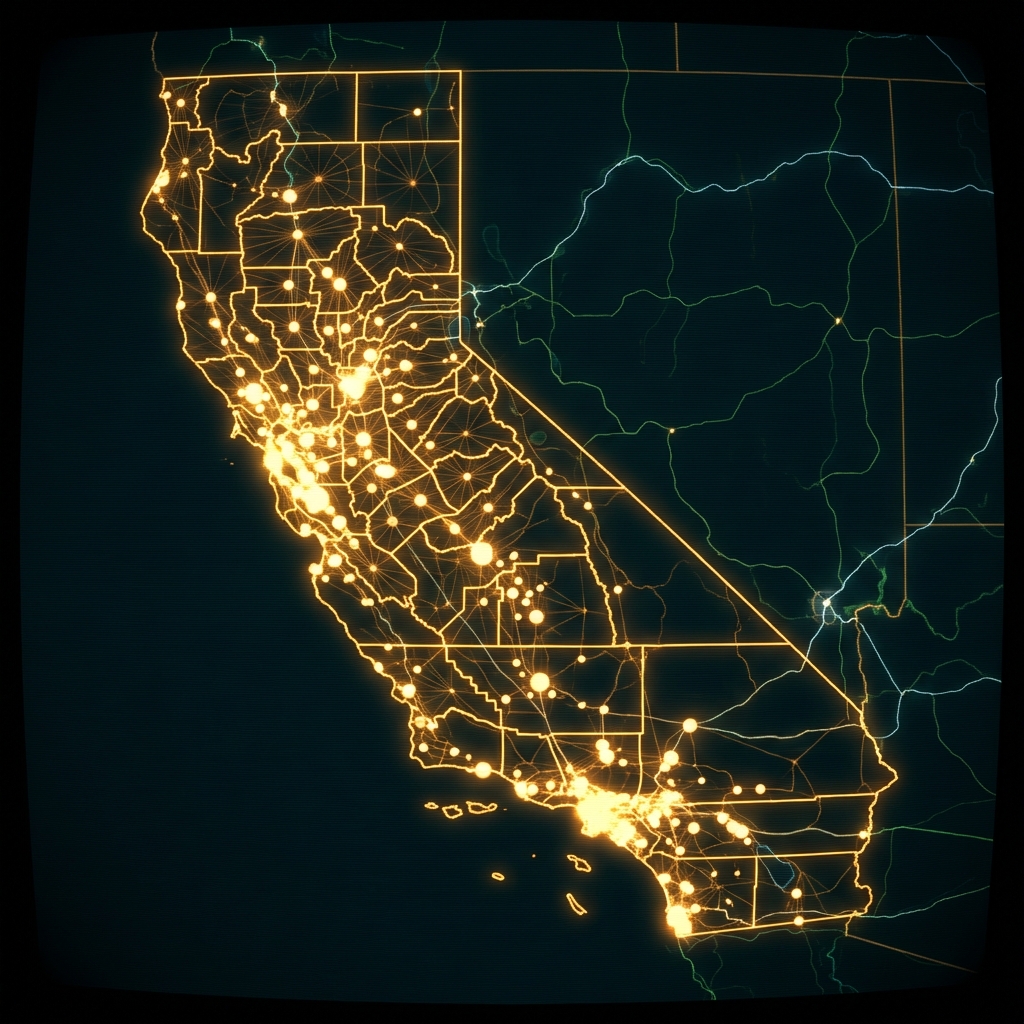
KYB Verification for Hospital Vendor Onboarding
A fintech platform onboarding a hospital as a commercial banking client cross-references the institution's NPI and CCN against this dataset to confirm its physical address, facility type, and government program participation history before approving a credit line.
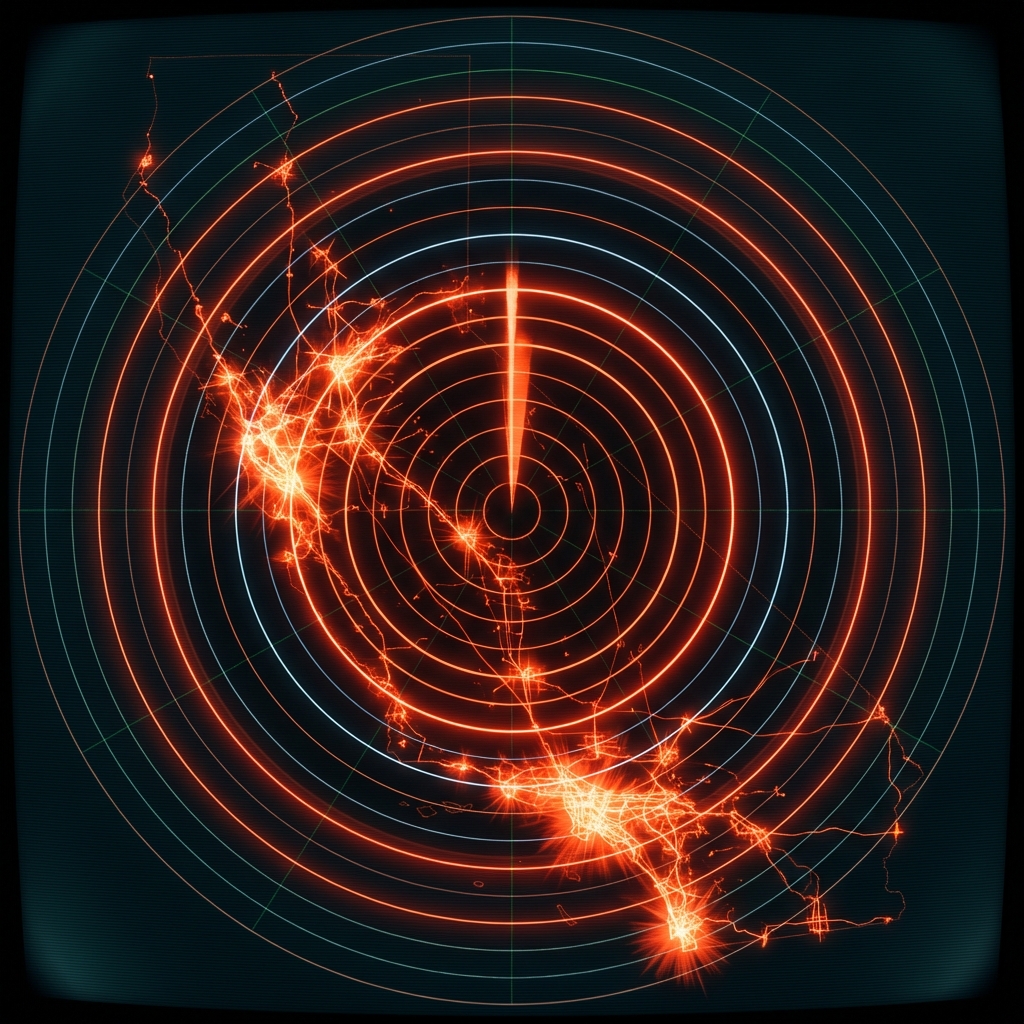
Healthcare Insurance Underwriting for Cyber Liability
An underwriter assessing cyber liability exposure for a hospital network uses the EHR adoption timeline and total incentive payments received to gauge how long the institution has operated certified digital health records systems, which informs the likelihood of legacy system vulnerabilities.